Project Description
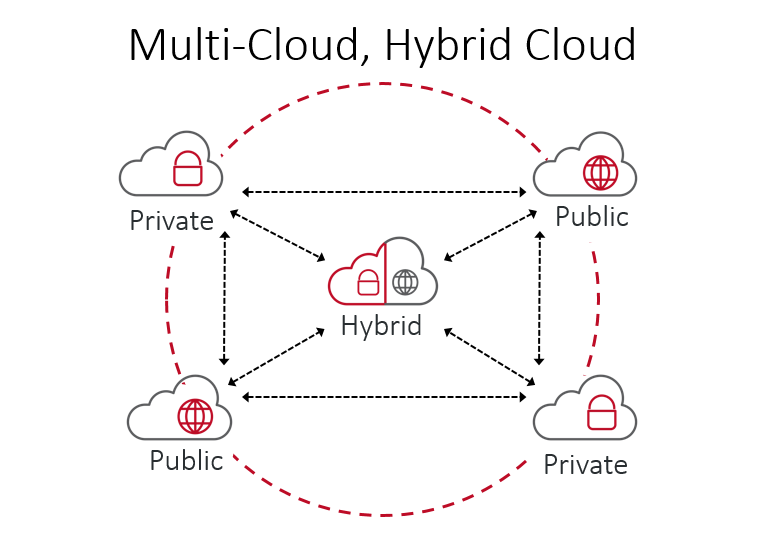
Hybrid Multi-Cloud Services
Customer Need
The client wanted to deploy Hybrid Multi-Cloud Services to support virtualized High Performance Computing (vHPC) applications. The client wanted to expand the operation of multiple existing client owned and managed data centers (on-premise) with two commercial cloud providers (Amazon Web Services and Microsoft Azure) seamlessly as one private cloud. The Hybrid Multi-Cloud architecture needed to allow for deployment as instances operating at different Information Levels (IL) and Protection Levels (PL) of security (i.e., IL-4, IL-5, IL-6, PL-2, PL-3, etc…). Each instance needed to support operation as an isolated enclave environment.
Issues
The client had four significant areas of concern:
- Security – Enforce network isolation of compute and storage resources between users of the system.
- Cybersecurity – Mandatory compliance with cybersecurity requirements was essential to meet continuous evaluation / certification of the Hybrid Multi-Cloud instances.
- Portability – Support the ability to deploy and migrate compute resources between Data Centers (on-premise and commercial cloud providers).
- Availability – Deliver highly available services to users of the system.
Solution
The client worked with Red Rake to extend the existing on-premise Data Centers to both AWS and Microsoft Azure commercial clouds. The client provisioned the required cloud accounts, Virtual Private networks (VPNs), subscriptions, and Software Defined Wide Area Network (SDWAN) to connect the on-premise Data Centers to AWS and Microsoft Azure. Red Rake designed and deployed the required cloud infrastructure – networking, security, and services – on the commercial cloud providers.
- Security – Red Rake designed and deployed the cloud subnets, Access Control Lists (ACLs), and Role Based Access Controls (RBACs) to enforce network security / isolation of compute and storage resources between users of the system.
- Cybersecurity – Red Rake configured systems and services to leverage existing cybersecurity services and best practices to ensure continuous compliance with cybersecurity requirements.
- Portability – Red Rake deployed processes, procedures, and machine images to support the migration of compute resources between Data Centers (on-premise and commercial cloud providers).
- Availability – Red Rake incorporated the use of multiple availability zones and regions within the commercial clouds to provide the client multiple high availability options.
Details
The client had experienced great success with their on-premise Data Centers but recognized the need to provide their users with the option of using commercial cloud providers. One key factor to success was the on-premise Data Centers worked together seamlessly. The client felt it was critical to maintain the seamless level of operation as they added commercial cloud resources.
Here are some highlights of the project.
Compute
- Compute Instances – Identified matching compute instances compatible with on-premise vHPC requirements.
- Machine Images – Leveraged hardened system images used on-premise in the cloud (Red Hat Enterprise Linux, Windows, Windows Server).
- Automation – Extended existing automation tools to support automated cloud deployments (Ansible / AWX, Terraform, bash / powershell scripts).
- Best Practices – Translated and updated existing compute best practices for use in the cloud (naming conventions, tags, operation standards, etc…).
Storage
- Block Storage / Direct Attached Storage (DAS) – Identified matching cloud storage services which met / exceeded on-premise vHPC performance.
- File Storage / Network Attached Storage (NAS) – Deployed standardized NAS services comparable to on-premise NAS capabilities.
- Object Storage / Simple Storage Service (S3) – Design and deployed an enterprise class AWS S3 reverse proxy service. Required for isolated enclave systems to seamlessly access AWS S3 storage (all on-premise and cloud based Data Centers). Interestingly, this capability enabled isolated enclave systems deployed on Microsoft Azure to seamlessly access AWS S3 storage using internal / private network only.
- Deduplication – Collaborated with multiple vendors (AWS, Microsoft, NetApp, and PureStorage) on data deduplication capable storage in the cloud. The client has a requirement to store petabytes of data. Data deduplication in the cloud would significantly reduce storage costs (3:1 could save 50% or more).
Networking
- Subnets – Designed and deployed network subnets which mirror the on-premise Data Center subnets (multiple / isolated user groups and core services).
- Access Control – Translated on-premise network access control security (VMware NSX) cloud through grouped subnets, Access Control Lists (ACLs), and routing rules.
- High Availability – Enabled deployment of high availability cloud based systems by extending the on-premise Data Center subnet design to leverage multiple availability zones and multiple regions offered by the cloud providers.
- Multicast – Worked with cloud providers and third-party vendors to enable multiple / isolated multicast subnets within cloud environments (a non-trivial task).
- Best Practices – Translated and updated existing network best practices for use in the cloud (naming conventions, tags, operation standards, etc…).
Security
- Multi-Factor Authentication (MFA) – Integrated cloud based resources with existing on-premise Data Center MFA security services (Active Directory, RSA Authentication Manager). Ensured seamless user login experience across on-premise and cloud based resources.
- Role Based Access Controls (RBAC) – Leveraged existing on-premise Data Center RBAC security (i.e., Active Directory users and security groups) with cloud based resources.
- Cloud Identity Access Management (IAM) – Mirrored existing on-premise Data Centers IAM with cloud IAM to ensure requirements were met while simplifying administration and management. Note: Some resources require use of cloud IAM.
- Best Practices – Translated and updated existing security best practices for use in the cloud (naming conventions, operation standards, etc…).
Services
- Cybersecurity – Integrated all cloud resources with existing on-premise Data Center cybersecurity services (scanning, patching, logging, auditing, etc…).
- Secure Data Transfer (SDT) – Designed and deployed efficient and trustworthy SDT capability within / between Data Centers (internal transfers) and between isolated enclaves (external transfers). Leveraged cloud provider object storage replication capabilities (S3 and Blob).
- Domain Name System (DNS) – Integrated existing on-premise Data Center DNS (high availability / multiple zones) with cloud DNS capabilities. Integration (DNS forwarding) was required to access some cloud service endpoints.
- Certificate Authority – Integrated existing on-premise Data Center Root / Intermediate / Issuer Certificate Authority (CA) with cloud CAs. This ensured seamless user experience / access to cloud service endpoints and the AWS S3 reverse proxy server.
- Monitoring – Ensured all cloud resources were configured to integrate into the existing on-premise Data Center monitoring services (network routing, firewalls, ports, and protocols).
- Billing – Costs for cloud services needed to be allocated to the appropriate user. A set of best practices (naming conventions, resource tags) was established to allocate cloud service costs to the appropriate user.
- Documentation – Created and updated extensive documentation on commercial cloud provider services / applications, and the design, usage, operation, and management of the Hybrid Multi-Cloud architecture. The documentation was targeted for use by users and system administrators.
Technologies
- Active Directory
- Apache
- Amazon Web Services
- Ansible / AWX
- Bash
- CentOS Linux
- Certificate Authority
- Containers
- Cloud Identity Access Management
- Microsoft Azure
- Microsoft Windows
- MySQL
- Network Appliance
- PHP
- PostgreSQL
- Powershell
- PureStorage
- Red Hat Enterprise Linux
- Syslog Server
- Terraform
- VMware vSphere
- Wiki / Media Wiki
Results
The initial release of the project was completed on time and within budget. The client continues to expand and evolve the delivered Hybrid Multi-Cloud Services as they acquire new users.